Understanding the Language of the Internet: A Deep Dive into Networking Protocols
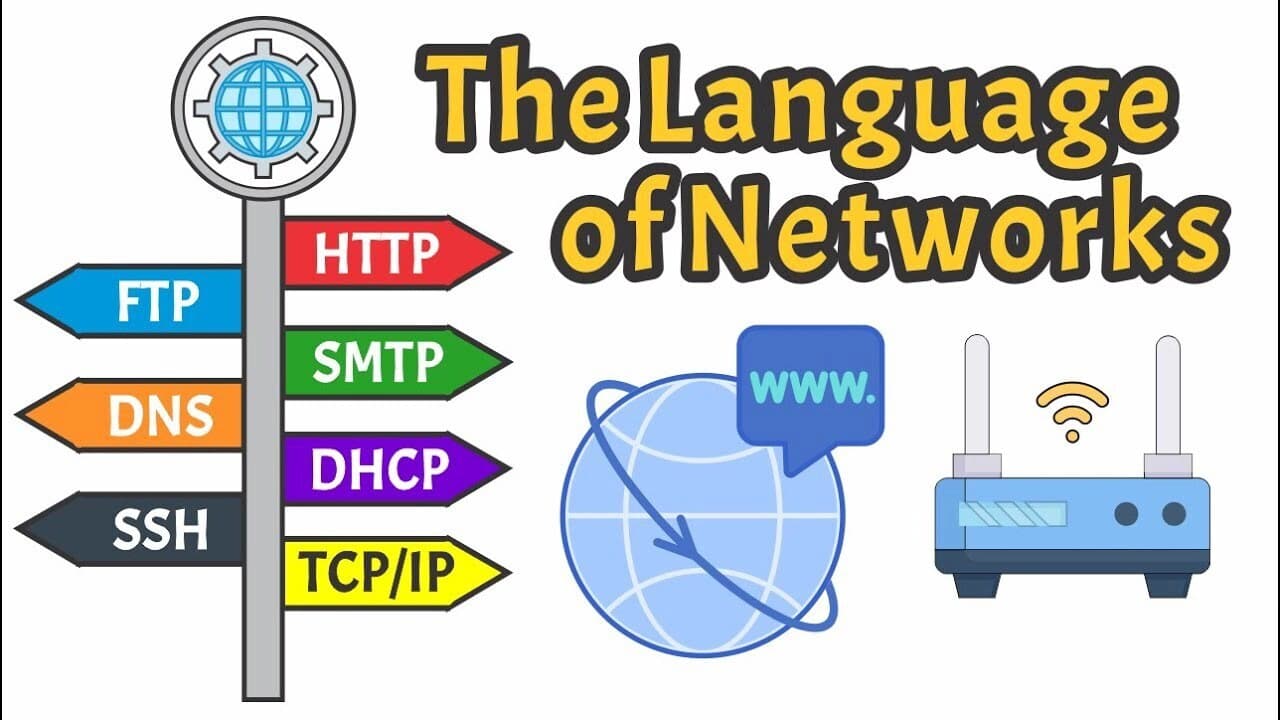
In our increasingly connected world, data flows seamlessly across vast networks, enabling everything from Browse the web to sending emails. But how does all this information travel so efficiently and reliably? The answer lies in networking protocols – a set of rules that govern how data is formatted, transmitted, and received across networks.
Think of protocols as the common languages that different computers speak to understand each other. Without them, the internet as we know it simply wouldn't exist. Let's break down some of the most fundamental networking protocols and explore their roles with real-world examples.
1. HTTP: The Foundation of the Web
Protocol Name: HTTP (Hypertext Transfer Protocol) Description: Used by web browsers and servers to communicate and exchange information.
HTTP is the unsung hero of your daily internet experience. Every time you type a website address into your browser, you're initiating an HTTP request.
Example: When you visit www.google.com, your web browser sends an HTTP request to Google's servers. The server then responds with the HTML, CSS, and JavaScript files that make up the Google homepage, which your browser renders for you to see. It's a stateless protocol, meaning each request from the client to the server is independent.
2. HTTPS: Securing Your Online Interactions
Protocol Name: HTTPS (Hypertext Transfer Protocol Secure) Description: An extension of HTTP that offers secure and encrypted communication.
HTTPS is the secure version of HTTP. It adds a layer of encryption (SSL/TLS) to protect your data from eavesdropping and tampering. You'll often see a padlock icon in your browser's address bar when a website uses HTTPS.
Example: When you log into your online banking account or make a purchase on an e-commerce site, HTTPS ensures that your sensitive information, like passwords and credit card numbers, is encrypted as it travels between your computer and the server, preventing unauthorized access.
3. FTP: Transferring Files with Ease
Protocol Name: FTP (File Transfer Protocol) Description: Used to transfer files between a client and a server.
FTP has been a long-standing method for moving files between computers over a network. While often superseded by more secure alternatives for general web content, it's still used in specific scenarios.
Example: A web developer might use FTP to upload website files (HTML, images, scripts) from their local computer to a web hosting server. Similarly, you might use an FTP client to download large software packages from a remote server.
4. TCP: Ensuring Reliable Data Delivery
Protocol Name: TCP (Transmission Control Protocol) Description: Delivers a stream of ordered bytes from one computer to another.
TCP is a connection-oriented protocol that provides reliable, ordered, and error-checked delivery of a stream of bytes between applications. It ensures that data reaches its destination completely and in the correct sequence.
Example: When you're streaming a video on YouTube, TCP is working behind the scenes to ensure that all the video data packets arrive in the correct order, so you don't experience a jumbled or incomplete video. If a packet is lost, TCP will request its retransmission.
5. IP: The Internet's Addressing System
Protocol Name: IP (Internet Protocol) Description: Addresses and routes packets of data sent between networked devices.
IP is the backbone of the internet, responsible for addressing and routing data packets. Every device connected to a network has an IP address, which is like its unique postal address.
Example: When you send an email, your computer uses IP to determine the recipient's email server's IP address. The email data is then broken down into packets, and IP helps route these packets across various routers and networks until they reach their destination.
6. UDP: Fast but Unreliable
Protocol Name: UDP (User Datagram Protocol) Description: A simple and connectionless protocol that does not divide messages into packets and sends them in order.
Unlike TCP, UDP is a connectionless protocol, meaning it doesn't establish a persistent connection or guarantee delivery. It's faster because it has less overhead, but it sacrifices reliability for speed.
Example: UDP is commonly used for real-time applications where speed is more critical than guaranteed delivery, such as online gaming or live video conferencing. If a few packets are lost in a game, it might result in a minor glitch, but the game continues without significant interruption.
7. SMTP: The Mailman of the Internet
Protocol Name: SMTP (Simple Mail Transfer Protocol) Description: Used to transmit emails across IP networks.
SMTP is the protocol that allows you to send emails. When you hit "send" on an email, SMTP takes over to deliver your message to the recipient's mail server.
Example: When you send an email from your Gmail account to a friend using Outlook, your Gmail server uses SMTP to communicate with your friend's Outlook server to deliver the email.
8. SSH: Secure Remote Access
Protocol Name: SSH (Secure Shell) Description: A cryptographic network protocol to secure data communication, remote command-line login, and remote command execution between two networked computers.
SSH provides a secure channel over an unsecured network by using strong encryption. It's widely used by network administrators and developers to access and manage remote servers.
Example: A system administrator might use SSH to securely log into a remote server located in a data center to perform maintenance, install software, or troubleshoot issues, all without the risk of their commands or data being intercepted.
Why are Protocols So Important?
These protocols, and many others, work together in a layered fashion (often referred to as the TCP/IP model or OSI model) to ensure that data travels efficiently and reliably across the globe. They provide the necessary structure, rules, and standards that allow diverse devices and systems to communicate effectively, making the internet the powerful tool it is today. Understanding these fundamental protocols is key to grasping how our digital world functions.